When using the Seed Fetcher to deploy Kubernetes Followers, an error occurs in the Seed Fetcher container. You check the logs and discover that although the Seed Fetcher was able to authenticate, it shows a 500 error in the log and does not successfully retrieve a seed file. What is the cause?
When loading policy, you receive a 422 Response from Conjur with a message.
What could cause this issue?
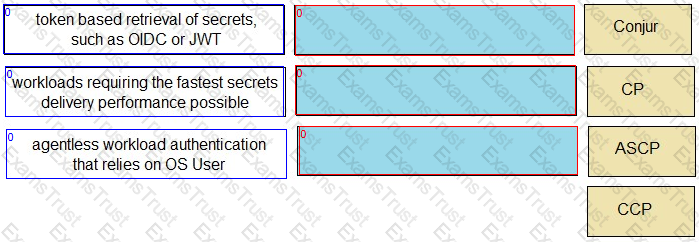
Match each scenario to the appropriate Secrets Manager solution.
While troubleshooting an issue with accounts not syncing to Conjur, you see this in the log file:
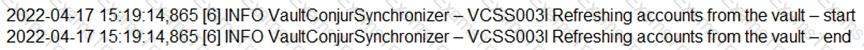
What could be the issue?
During the configuration of Conjur, what is a possible deployment scenario?
When installing the Vault Conjur Synchronizer, you see this error:
Forbidden
Logon Token is Empty – Cannot logon
Unauthorized
What must you ensure to remediate the issue?
What is a possible Conjur node role change?
When working with Credential Providers in a Privileged Cloud setting, what is a special consideration?
A customer wants to ensure applications can retrieve secrets from Conjur in three different data centers if the Conjur Leader becomes unavailable. Conjur Followers are already deployed in each of these data centers.
How should you architect the solution to support this requirement?
In a 3-node auto-failover cluster, the Leader has been brought down for patching that lasts longer than the configured TTL. A Standby has been promoted.
Which steps are required to repair the cluster when the old Leader is brought back online?
A customer wants to minimize the Kubernetes application code developers must change to adopt Conjur for secrets access.
Which solutions can meet this requirement? (Choose two.)
You have a request to protect all the properties around a credential object. When configuring the credential in the Vault, you specified the address, user and password for the credential.
How do you configure the Vault Conjur Synchronizer to properly sync all properties?
What is the correct process to upgrade the CCP Web Service?
You have a PowerShell script that is being used on 1000 workstations. It requires a Windows Domain credential that is currently hard coded in the script.
What is the simplest solution to remove that credential from the Script?
You are diagnosing this log entry:
From Conjur logs:
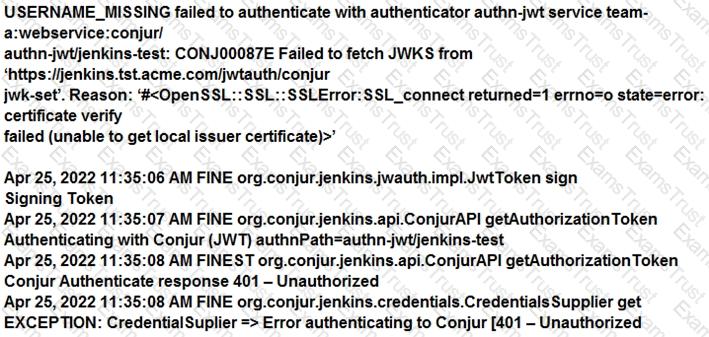
Given these errors, which problem is causing the breakdown?
What is the correct command to import the root CA certificate into Conjur?
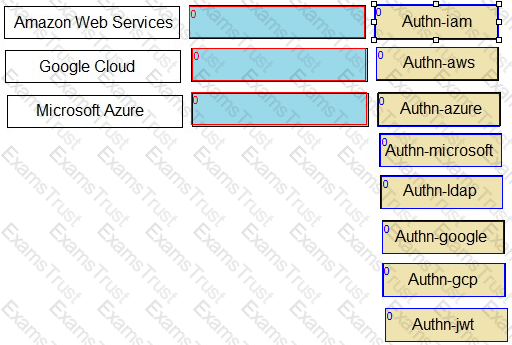
Match each cloud platform to the correct Conjur authenticator.
A Kubernetes application attempting to authenticate to the Follower load balancer receives this error:
ERROR: 2024/10/30 06:07:08 authenticator.go:139: CAKC029E Received invalid response to certificate signing request. Reason: status code 401
When checking the logs, you see this message:
authn-k8s/prd-cluster-01 is not enabled
How do you remediate the issue?