Based on the information in the case study, which security team should be the most suitable to perform root cause analysis of the attack and present the proposal to solve the challenges faced by theA .R.T.I.E.organization?
The cybersecurity team performed a quantitative risk analysis onA .R.T.I.E.'s IT systems during the risk management process.
What is the focus of a quantitative risk analysis?
During analysis, the Dell Services team found outdated applications and operating systems with missing security patches. To avert potential cyberattacks, Dell recommends application and operating system hardening measures.
Why is security hardening important for A.R.T.I.E .?
Which framework should be recommended toA .R.T.I.E.to enhance the overall security and resilience of their critical infrastructure, and outline methods to reduce their cybersecurity risk?
AR.T.I.E.'s business is forecast to grow tremendously in the next year, the organization will not only need to hire new employees but also requires contracting with third-party vendors to continue seamless operations.A .R.T.I.E.uses a VPN to support its employees on the corporate network, but the organization is facing a security challenge in supporting the third-party business vendors.
To better meetA .R.T.I.E.'s security needs, the cybersecurity team suggested adopting a Zero Trust architecture (ZTA). The main aim was to move defenses from static, network-based perimeters to focus on users, assets, and resources. Zero Trust continuously ensures that a user is authentic and the request for resources is also valid. ZTA also helps to secure the attack surface while supporting vendor access.
What is the main challenge that ZTA addresses?
A .R.T.I.E.has an evolving need, which was amplified during the incidents. Their complex and dispersed IT environments have thousands of users, applications, and resources to manage. Dell found that the existing Identity and Access Management was limited in its ability to apply expanding IAM protection to applications beyond the core financial and human resource management application.A .R.T.I.E.also did not have many options for protecting their access especially in the cloud.A .R.T.I.E.were also not comfortable exposing their applications for remote access.
Dell recommended adopting robust IAM techniques like mapping out connections between privileged users and admin accounts, and the use multifactor authentication.
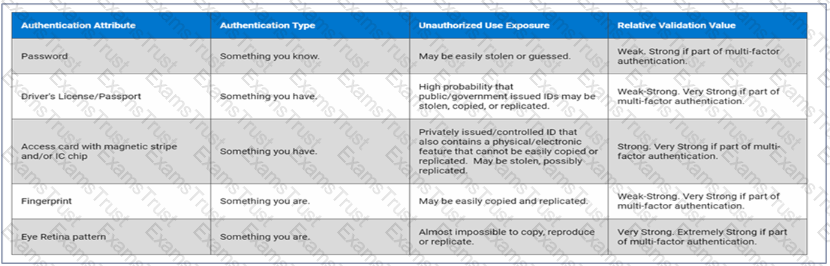
The Dell Services team suggest implementing a system that requires individuals to provide a PIN and biometric information to access their device.
Which type of multifactor authentication should be suggested?