You need to meet the planned changes and technical requirements for App1.
What should you implement?
You create a Log Analytics workspace.
You need to implement the technical requirements for auditing.
What should you configure in Azure AD?
You need to meet the technical requirements for the probability that user identities were compromised.
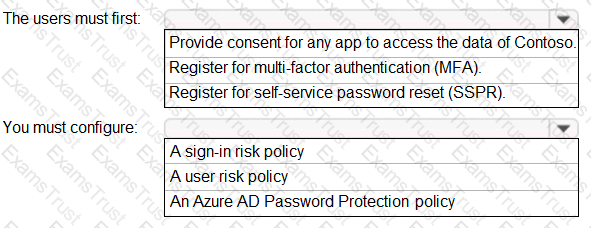
What should the users do first, and what should you configure? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
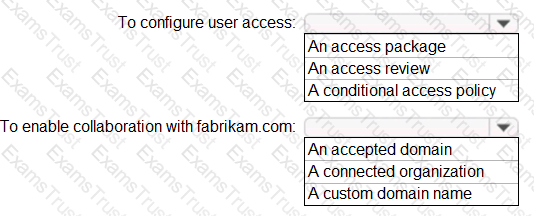
You need to implement the planned changes and technical requirements for the marketing department.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
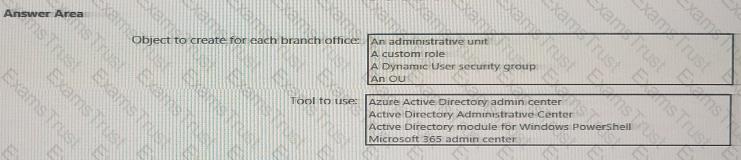
You need to meet the technical requirements for license management by the helpdesk administrators.
What should you create first, and which tool should you use? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to locate licenses to the A. Datum users. The solution must need the technical requirements.
Which type of object should you create?
You need to sync the ADatum users. The solution must meet the technical requirements.
What should you do?
You need to meet the planned changes for the User administrator role.
What should you do?
You need to allocate licenses to the new users from A. Datum. The solution must meet the technical requirements.
Which type of object should you create?
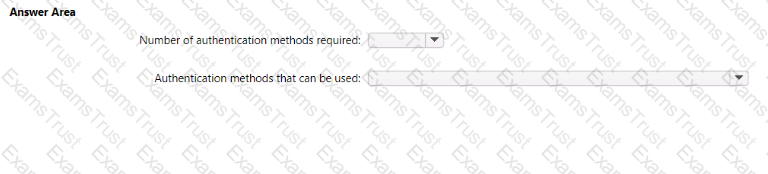
You need to meet the technical requirements for the probability that user identifies were compromised.
What should the users do first, and what should you configure? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.

You need to implement the planned changes for litware.com. What should you configure?
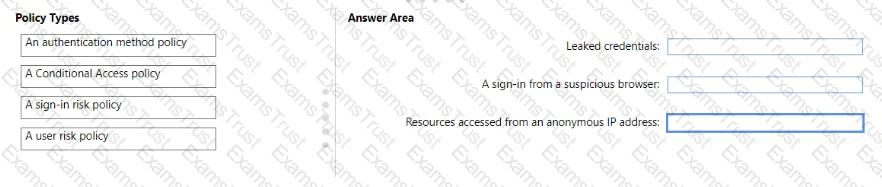
You need to resolve the recent security incident issues.
What should you configure for each incident? To answer, drag the appropriate policy types to the correct issues. Each policy type may be used once, more than once, or not at all. You may need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
You need to modify the settings of the User administrator role to meet the technical requirements. Which two actions should you perform for the role? Each correct answer presents part of the solution. NOTE: Each correct selection is worth one point.
You implement the planned changes for SSPR.
What occurs when User3 attempts to use SSPR? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to resolve the issue of the sales department users. What should you configure for the Azure AD tenant?
You need implement the planned changes for application access to organizational data. What should you configure?
You need to implement the planned changes for Package1. Which users can create and manage the access review?
You need to resolve the issue of the guest user invitations. What should you do for the Azure AD tenant?
You need to resolve the issue of I-.Group1. What should you do first?
You need to configure the detection of multi-staged attacks to meet the monitoring requirements.
What should you do?
You need to track application access assignments by using Identity Governance. The solution must meet the delegation requirements.
What should you do first?
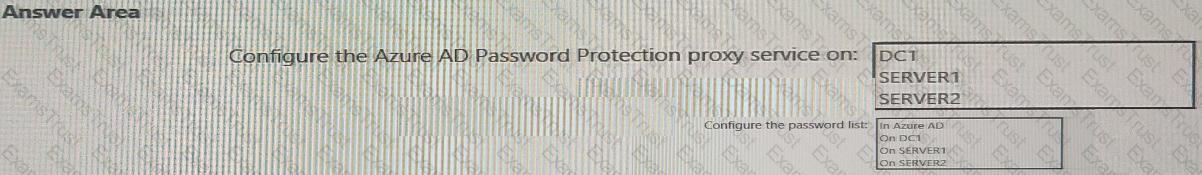
You need to implement password restrictions to meet the authentication requirements.
You install the Azure AD password Protection DC agent on DC1.
What should you do next? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
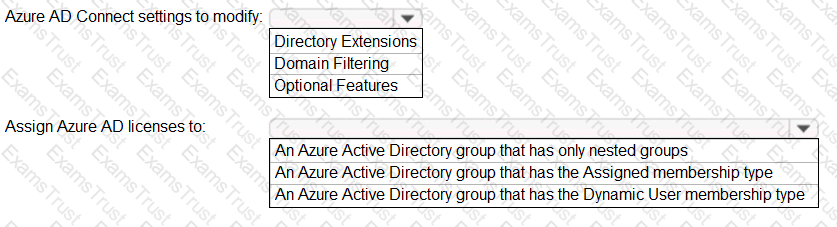
You need to configure the assignment of Azure AD licenses to the Litware users. The solution must meet the licensing requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
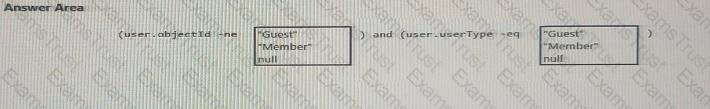
You need to create the LWGroup1 group to meet the management requirements.
How should you complete the dynamic membership rule? To answer, drag the appropriate values to the correct targets. Each value may be used once, more than once, or not at all. You many need to drag the split bar between panes or scroll to view content.
NOTE: Each correct selection is worth one point.
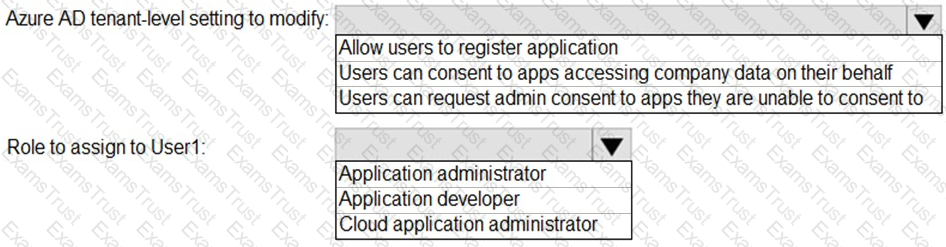
You need to configure app registration in Azure AD to meet the delegation requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
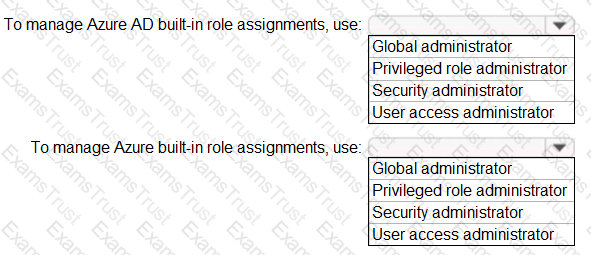
You need to identify which roles to use for managing role assignments. The solution must meet the delegation requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
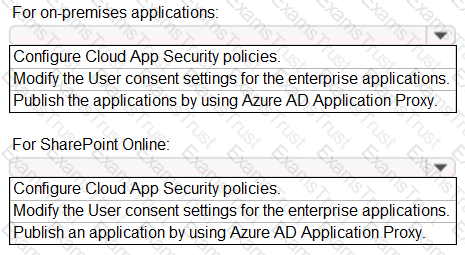
You need to implement on-premises application and SharePoint Online restrictions to meet the authentication requirements and the access requirements.
What should you do? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You need to configure the detection of multi staged attacks to meet the monitoring requirements.
What should you do?
You need to configure the MFA settings for users who connect from the Boston office. The solution must meet the authentication requirements and the access requirements.
What should you configure?
You need to meet the authentication requirements for leaked credentials.
What should you do?
You have an Azure Active Directory (Azure AD) tenant named conto.so.com that has Azure AD Identity Protection enabled. You need to Implement a sign-in risk remediation policy without blocking access.
What should you do first?
You have an Azure subscription, a Google Cloud Platform (GCP) account, and an Amazon Web Services (AWS) account.
You need to recommend a solution to assess the risks associated with privilege assignments across all the platforms. The solution must minimize administrative effort
What should you include in the recommendation?
You have a Microsoft 365 tenant.
All users have mobile phones and laptops.
The users frequently work from remote locations that do not have Wi-Fi access or mobile phone connectivity.
While working from the remote locations, the users connect their laptop to a wired network that has internet
access.
You plan to implement multi-factor authentication (MFA).
Which MFA authentication method can the users use from the remote location?
You have a Microsoft 365 tenant.
All users have mobile phones and laptops.
The users frequently work from remote locations that do not have Wi-Fi access or mobile phone connectivity. While working from the remote locations, the users connect their laptop to a wired network that has internet access.
You plan to implement multi-factor authentication (MFA).
Which MFA authentication method can the users use from the remote location?
You have an Azure subscription named Sub1 that contains a resource group named RG1. RG1 contains an Azure Cosmos DB database named DB1 and an Azure Kubernetes Service (AKS) cluster named AKS1. AKS1 uses a managed identity.
You need to ensure that AKS1 can access DB1. The solution must meet the following requirements:
• Ensure that AKS1 uses the managed identity to access DB1.
• Follow the principle of least privilege.
Which role should you assign to the managed identity of AKS1.
Your network contains an on-premises Active Directory domain named contoso.com. The domain contains the objects shown in the following table.
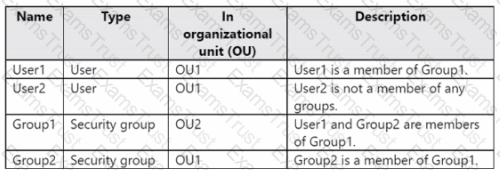
You install Microsoft Entra Connect. You configure the Domain and OU filtering settings as shown in the Domain and OU Filtering exhibit. (Click the Domain and OU Filtering tab.)
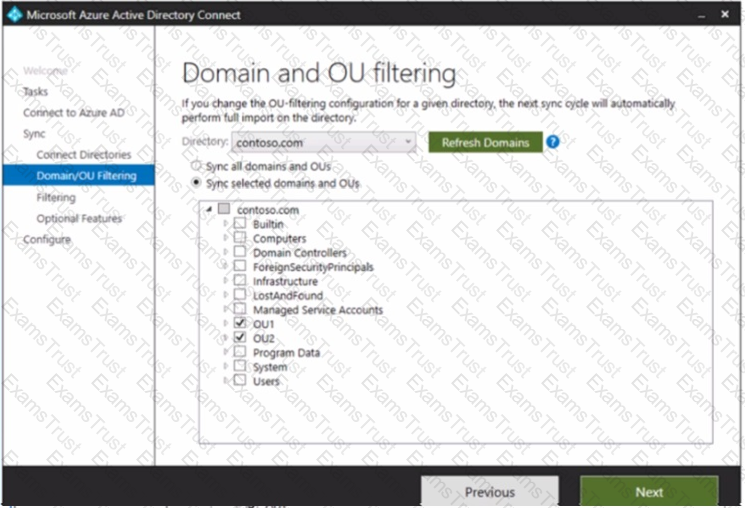
You configure the Filter users and devices settings as shown in the Filter Users and Devices exhibit. (Click the Filter Users and Devices tab.)
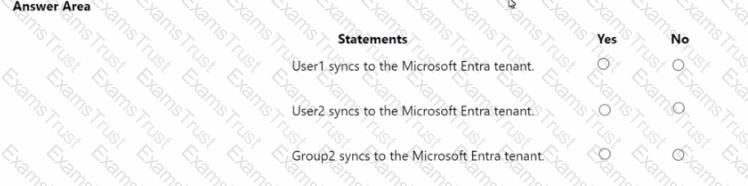
For each of the following statements, select Yes if the statement is true. Otherwise, select No.
NOTE: Each correct selection is worth one point.
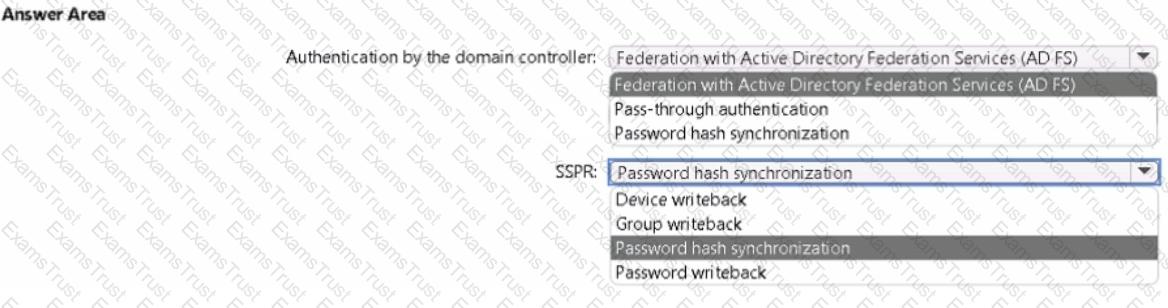
Your on-premises network contains an Active Directory domain that uses Azure AD Connect to sync with an Azure AD tenant. You need to configure Azure AD Connect to meet the following requirements:
• User sign-ins to Azure AD must be authenticated by an Active Directory domain controller.
• Active Directory domain users must be able to use Azure AD self-service password reset (SSPR).
What should you use for each requirement? To answer, select the appropriate options in the answer area.
NOTE: Each correct selection is worth one point.
You have 2,500 users who are assigned Microsoft Office 365 Enterprise E3 licenses. The licenses are assigned to individual users.
From the Groups blade in the Azure Active Directory admin center, you assign Microsoft 365 Enterprise E5 licenses to the users.
You need to remove the Office 365 Enterprise E3 licenses from the users by using the least amount of administrative effort.
What should you use?
Task 9
You need to ensure that when users in the Sg-Operations group go to the My Apps portal a tab named Operations appears that contains only the following applications:
• Unkedln
• Box
Task 7
You need to lock out accounts for five minutes when they have 10 failed sign-in attempts.
Task 2
You need to implement a process to review guest users who have access to the Salesforce app. The review must meet the following requirements:
• The reviews must occur monthly.
• The manager of each guest user must review the access.
• If the reviews are NOT completed within five days, access must be removed.
• If the guest user does not have a manager, Megan Bowen must review the access.
Task 6
You need to implement additional security checks before the members of the Sg-Executive can access any company apps. The members must meet one of the following conditions:
• Connect by using a device that is marked as compliant by Microsoft Intune.
• Connect by using client apps that are protected by app protection policies.
Task 10
You need to create a group named Audit. The solution must ensure that the members of Audit can activate the Security Reader role.
Task 4
You need to ensure that all users can consent to apps that require permission to read their user profile. Users must be prevented from consenting to apps that require any other permissions.
Task 8
You need to prevent all users from using legacy authentication protocols when authenticating to Microsoft Entra ID.
Task 3
You need to add the Linkedln application as a resource to the Sales and Marketing access package. The solution must NOT remove any other resources from the access package.
Task 1
You need to deploy multi factor authentication (MFA). The solution must meet the following requirements:
• Require MFA registration only for members of the Sg-Finance group.
• Exclude Debra Berger from having to register for MFA.
• Implement the solution without using a Conditional Access policy.
Task 5
You need to assign a Windows 10/11 Enterprise E3 license to the Sg-Retail group.