What is the order of steps to create a custom network policy?
(Drag the steps into the correct order of occurrence, from the first step to the last.)

A Prisma Cloud Administrator needs to enable a Registry Scanning for a registry that stores Windows images. Which of the following statement is correct regarding this process?
An administrator has deployed Console into a Kubernetes cluster running in AWS. The administrator also has configured a load balancer in TCP passthrough mode to listen on the same ports as the default Prisma Compute Console configuration.
In the build pipeline, the administrator wants twistcli to talk to Console over HTTPS. Which port will twistcli need to use to access the Prisma Compute APIs?
An organization wants to be notified immediately to any “High Severity” alerts for the account group “Clinical Trials” via Slack.
Which option shows the steps the organization can use to achieve this goal?
How often do Defenders share logs with Console?
Which role must be assigned to DevOps users who need access to deploy Container and Host Defenders in Compute?
While writing a custom RQL with array objects in the investigate page, which type of auto-suggestion a user can leverage?
Which two offerings will scan container images in Jenkins pipelines? (Choose two.)
A manager informs the SOC that one or more RDS instances have been compromised and the SOC needs to make sure production RDS instances are NOT publicly accessible.
Which action should the SOC take to follow security best practices?
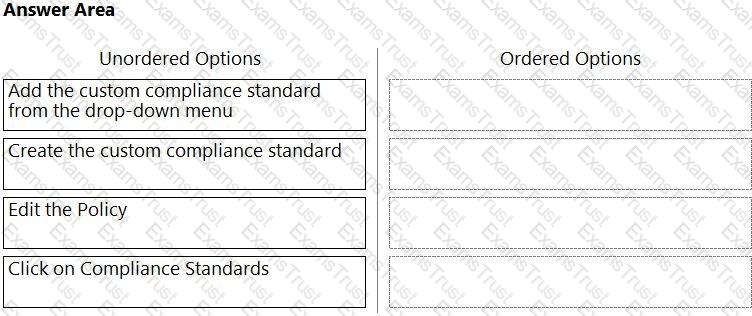
Which order of steps map a policy to a custom compliance standard?
(Drag the steps into the correct order of occurrence, from the first step to the last.)
How is the scope of each rule determined in the Prisma Cloud Compute host runtime policy?
A customer wants to harden its environment from misconfiguration.
Prisma Cloud Compute Compliance enforcement for hosts covers which three options? (Choose three.)
Which serverless cloud provider is covered by the "overly permissive service access" compliance check?
Console is running in a Kubernetes cluster, and Defenders need to be deployed on nodes within this cluster.
How should the Defenders in Kubernetes be deployed using the default Console service name?
Which three Orchestrator types are supported when deploying Defender? (Choose three.)
What is the primary purpose of Prisma Cloud Code Security?
Which step should a SecOps engineer implement in order to create a network exposure policy that identifies instances accessible from any untrusted internet sources?
An administrator has been tasked with creating a custom service that will download any existing compliance report from a Prisma Cloud Enterprise tenant.
In which order will the APIs be executed for this service?
(Drag the steps into the correct order of occurrence, from the first step to the last.)

Which two variables must be modified to achieve automatic remediation for identity and access management (IAM) alerts in Azure cloud? (Choose two.)
Which statement is true regarding CloudFormation templates?
The Compute Console has recently been upgraded, and the administrator plans to delay upgrading the Defenders and the Twistcli tool until some of the team’s resources have been rescaled. The Console is currently one major release ahead.
What will happen as a result of the Console upgrade?
The exclamation mark on the resource explorer page would represent?
A customer wants to monitor the company’s AWS accounts via Prisma Cloud, but only needs the resource configuration to be monitored for now.
Which two pieces of information do you need to onboard this account? (Choose two.)
When an alert notification from the alarm center is deleted, how many hours will a similar alarm be suppressed by default?
Which two services require external notifications to be enabled for policy violations in the Prisma Cloud environment? (Choose two.)
An administrator has access to a Prisma Cloud Enterprise.
What are the steps to deploy a single container Defender on an ec2 node?
A customer has a requirement to scan serverless functions for vulnerabilities.
What is the correct option to configure scanning?
Which of the following is not a supported external integration for receiving Prisma Cloud Code Security notifications?
Which options show the steps required after upgrade of Console?
Which ban for DoS protection will enforce a rate limit for users who are unable to post five (5) “. tar.gz" files within five (5) seconds?
A customer does not want alerts to be generated from network traffic that originates from trusted internal networks.
Which setting should you use to meet this customer’s request?
In WAAS Access control file upload controls, which three file types are supported out of the box? (Choose three.)
Which set of steps is the correct process for obtaining Console images for Prisma Cloud Compute Edition?
A customer has a requirement to terminate any Container from image topSecret:latest when a process named ransomWare is executed.
How should the administrator configure Prisma Cloud Compute to satisfy this requirement?
How many CLI remediation commands can be added in a custom policy sequence?
Which three options for hardening a customer environment against misconfiguration are included in Prisma Cloud Compute compliance enforcement for hosts? (Choose three.)
Which type of compliance check is available for rules under Defend > Compliance > Containers and Images > CI?
A customer wants to be notified about port scanning network activities in their environment. Which policy type detects this behavior?
Anomaly policy uses which two logs to identify unusual network and user activity? (Choose two.)
You are an existing customer of Prisma Cloud Enterprise. You want to onboard a public cloud account and immediately see all of the alerts associated with this account based off ALL of your tenant’s existing enabled policies. There is no requirement to send alerts from this account to a downstream application at this time.
Which option shows the steps required during the alert rule creation process to achieve this objective?
Which API calls can scan an image named myimage: latest with twistcli and then retrieve the results from Console?
What is the behavior of Defenders when the Console is unreachable during upgrades?
Which data security default policy is able to scan for vulnerabilities?
What is the default namespace created by Defender DaemonSet during deployment?
Which two filters are available in the SecOps dashboard? (Choose two.)
Which method should be used to authenticate to Prisma Cloud Enterprise programmatically?
What are two alarm types that are registered after alarms are enabled? (Choose two.)
Which two statements are true about the differences between build and run config policies? (Choose two.)
Which of the below actions would indicate – “The timestamp on the compliance dashboard?
What are the two ways to scope a CI policy for image scanning? (Choose two.)
Creation of a new custom compliance standard that is based on other individual custom compliance standards needs to be automated.
Assuming the necessary data from other standards has been collected, which API order should be used for this new compliance standard?
Which of the following is a reason for alert dismissal?
Which two bot types are part of Web Application and API Security (WAAS) bot protection? (Choose two.)
Given the following information, which twistcli command should be run if an administrator were to exec into a running container and scan it from within using an access token for authentication?
• Console is located at
• Token is: TOKEN_VALUE
• Report ID is: REPORTJD
• Container image running is: myimage:latest
Which command should be used in the Prisma Cloud twistcli tool to scan the nginx:latest image for vulnerabilities and compliance issues?
A)
B)
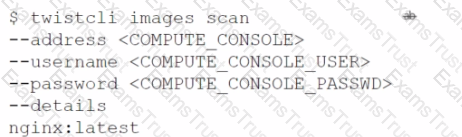
C)
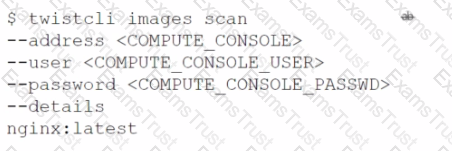
D)
The Unusual protocol activity (Internal) network anomaly is generating too many alerts. An administrator has been asked to tune it to the option that will generate the least number of events without disabling it entirely.
Which strategy should the administrator use to achieve this goal?
What are the subtypes of configuration policies in Prisma Cloud?
Which three actions are available for the container image scanning compliance rule? (Choose three.)
Which three options are selectable in a CI policy for image scanning with Jenkins or twistcli? (Choose three.)
Which report includes an executive summary and a list of policy violations, including a page with details for each policy?
Which type of query is used for scanning Infrastructure as Code (laC) templates?
Which three incident types will be reflected in the Incident Explorer section of Runtime Defense? (Choose three.)
An administrator has added a Cloud account on Prisma Cloud and then deleted it.
What will happen if the deleted account is added back on Prisma Cloud within a 24-hour period?
A container and image compliance rule has been configured by enabling all checks; however, upon review, the container's compliance view reveals only the entries in the image below.
What is the appropriate action to take next?
Which two CI/CD plugins are supported by Prisma Cloud as part of its Code Security? (Choose two.)
In Prisma Cloud Software Release 22.06 (Kepler), which Registry type is added?
Which step is included when configuring Kubernetes to use Prisma Cloud Compute as an admission controller?
What is the order of steps in a Jenkins pipeline scan?
(Drag the steps into the correct order of occurrence, from the first step to the last.)
What will happen when a Prisma Cloud Administrator has configured agentless scanning in an environment that also has Host and Container Defenders deployed?
Which alert deposition severity must be chosen to generate low and high severity alerts in the Anomaly settings when user wants to report on an unknown browser and OS, impossible time travel, or both due to account hijacking attempts?
A Prisma Cloud administrator is onboarding a single GCP project to Prisma Cloud. Which two steps can be performed by the Terraform script? (Choose two.)
In Azure, what permissions need to be added to Management Groups to allow Prisma Cloud to calculate net effective permissions?
Prisma Cloud supports which three external systems that allow the import of vulnerabilities and provide additional context on risks in the cloud? (Choose three.)
A user from an organization is unable to log in to Prisma Cloud Console after having logged in the previous day.
Which area on the Console will provide input on this issue?
On which cloud service providers can new API release information for Prisma Cloud be received?
What factor is not used in calculating the net effective permissions for a resource in AWS?
Which two elements are included in the audit trail section of the asset detail view? (Choose two).
A Prisma Cloud Administrator onboarded an AWS cloud account with agentless scanning enabled successfully to Prisma Cloud. Which item requires deploying defenders to be able to inspect the risk on the onboarded AWS account?